The healthcare landscape across the Colorado Front Range is experiencing a profound digital shift. From bustling family practices in Fort Collins and specialized clinics in Boulder to veterinary hospitals and dental offices in Greeley and Loveland, patient care now relies entirely on interconnected technology. Electronic Health Records (EHR), cloud-based patient portals, and automated billing systems have streamlined clinical operations, allowing providers to focus on what matters most: patient outcomes.
However, this rapid digital evolution comes with a severe warning. Medical and dental practices are now the primary targets for global cybercriminal syndicates. Patient data—formally known as Protected Health Information (PHI)—is exceptionally valuable on the dark web, often fetching ten times the price of a standard credit card number. A single data breach can expose financial records, medical histories, and social security numbers, making healthcare providers highly lucrative targets.
For independent practices in Northern Colorado, cybersecurity is no longer just a technical consideration managed by an occasional IT support person. It is a fundamental operational requirement and a legal mandate governed strictly by the Health Insurance Portability and Accountability Act (HIPAA).
Navigating the intersection of daily medical workflows, complex cloud architecture, and strict federal compliance demands an intentional, strategic approach to managed IT services.
The Reality of Healthcare Cyber Threats in the Front Range
Many independent medical and dental providers believe they are safely flying under the radar of major cyber threats, assuming that hackers only target massive hospital networks or national insurance providers. This assumption is a dangerous miscalculation.
In reality, cybercriminals actively exploit smaller, regional clinics precisely because they lack the multi-million dollar internal IT security departments of major health systems. Ransomware attacks, sophisticated phishing campaigns, and social engineering schemes frequently disrupt local practices across Larimer, Weld, and Boulder counties.
The True Cost of Downtime and Regulatory Sanctions
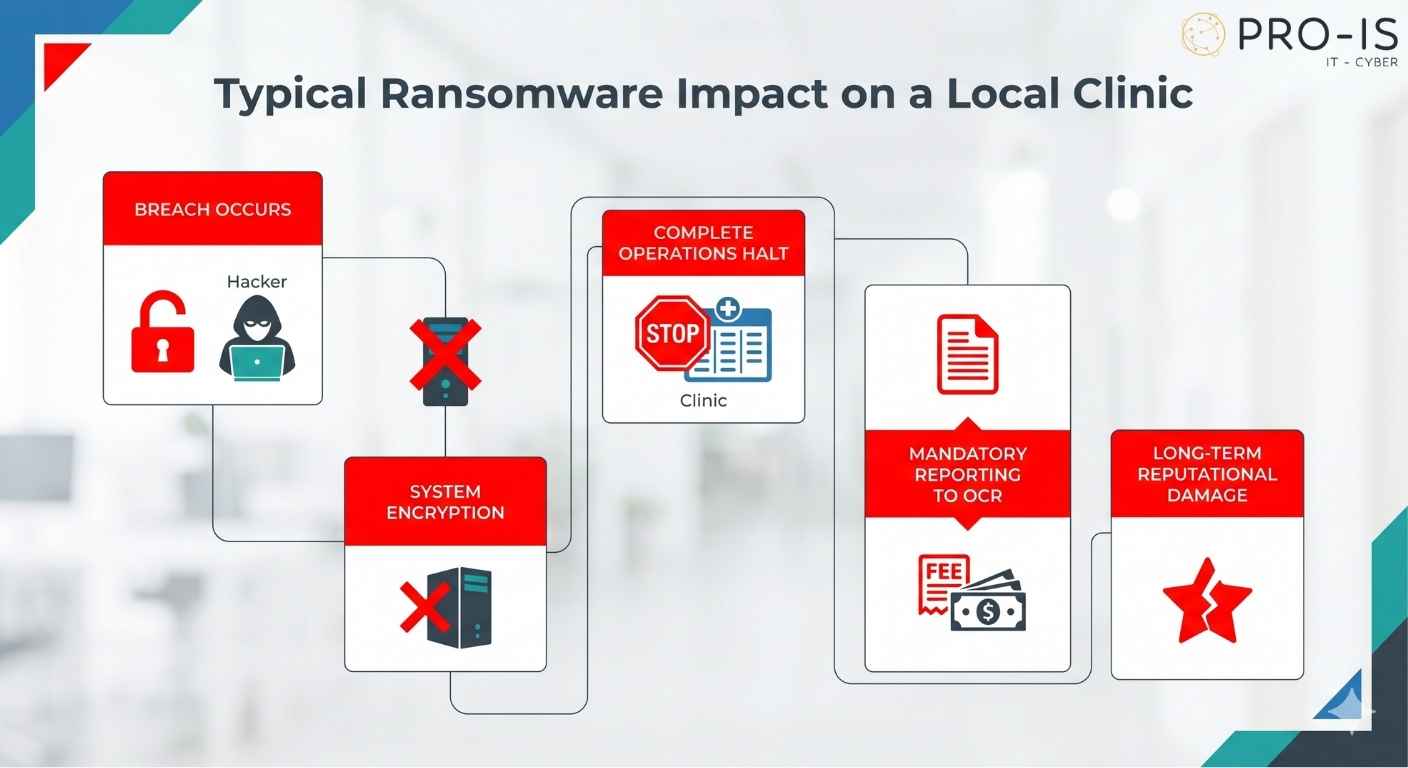
When a clinic falls victim to a ransomware attack, the consequences extend far beyond a temporary IT inconvenience:
- Clinical Paralysis: Digital schedules vanish, patient charts become entirely inaccessible, prescription systems go offline, and diagnostic equipment fails to communicate with workstations. The immediate result is forced closure, cancelled appointments, and compromised patient safety.
- The Financial Toll: Beyond the immediate loss of billable hours, the financial aftermath of an unmanaged data breach can threaten the survival of an independent practice.
Regulatory Penalties: The Department of Health and Human Services (HHS) Office for Civil Rights (OCR) actively investigates healthcare data breaches. Failing to demonstrate proactive compliance measures can result in catastrophic fines, even for first-time or accidental violations.
Demystifying HIPAA Security Rules for Modern IT Infrastructure
Achieving genuine HIPAA compliance requires shifting away from superficial checklists toward establishing a robust, continuous security posture. The HIPAA Security Rule explicitly requires covered entities to maintain appropriate administrative, physical, and technical safeguards to ensure the confidentiality, integrity, and security of electronic PHI (ePHI).
Technical Safeguards: Beyond the Basic Antivirus
Relying on a retail-grade firewall and basic antivirus software is entirely inadequate for safeguarding a modern healthcare network. A compliant technical architecture requires multi-layered, enterprise-grade defense mechanisms.
1. End-to-End Encryption
Any device that touches, transmits, or stores ePHI must utilize advanced encryption protocols, both at rest and in transit. If an employee laptop containing patient data is stolen from a vehicle in a local parking lot, a fully encrypted hard drive provides a safe harbor under the HIPAA Breach Notification Rule, preventing a costly public disclosure.
2. Strict Access Control and Unique User Identification
Sharing generic login accounts like “FrontDesk” or “NurseStation” violates core HIPAA standards. Every staff member must possess distinct, auditable login credentials. Furthermore, implementing Multi-Factor Authentication (MFA) is mandatory. MFA ensures that even if an employee falls victim to a phishing email, an attacker cannot access the internal clinical network without a secondary authentication factor.
3. Comprehensive Audit Controls
Compliance demands proof. Your network must run specialized software that continuously logs all user activity, tracking exactly who accesses, modifies, or deletes patient files. In the event of an audit or an unauthorized access scare, these logs are vital for demonstrating accountability.
The Strategic Importance of Business Continuity and Hybrid Cloud Backups
In healthcare IT, data backup is not merely an insurance policy—it is a critical compliance mandate. The HIPAA Security Rule explicitly dictates that practices must establish a reliable contingency plan, including an exact data backup plan and a comprehensive disaster recovery strategy.
The Pitfalls of Inadequate Backup Systems
Many local clinics mistakenly believe their backup strategy is secure because they plug an external hard drive into a server every Friday or use a consumer-grade cloud storage application. These methods introduce severe vulnerabilities:
Ransomware Vulnerability: Local external drives attached directly to a network are immediately found and encrypted by modern ransomware strains.
Lack of Testing: Unmonitored backup systems frequently fail silently due to software conflicts or disk capacity errors, leaving the practice with corrupted, unrecoverable data when an emergency occurs.
The Pro-IS Standard: Resilient Hybrid Cloud Solutions
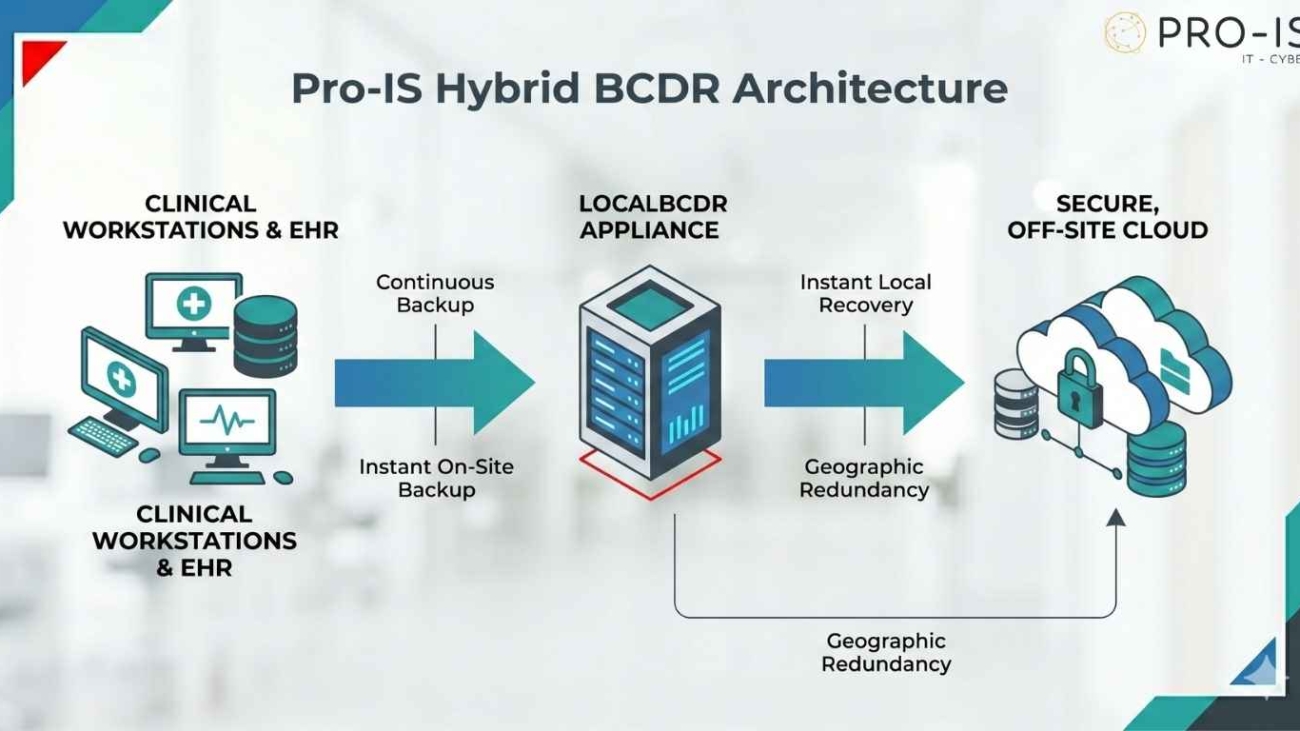
Pro-IS protects Northern Colorado practices by deploying highly resilient Business Continuity and Disaster Recovery (BCDR) systems. This strategic approach utilizes a hybrid architecture combining on-site appliances with secure, encrypted cloud data centers
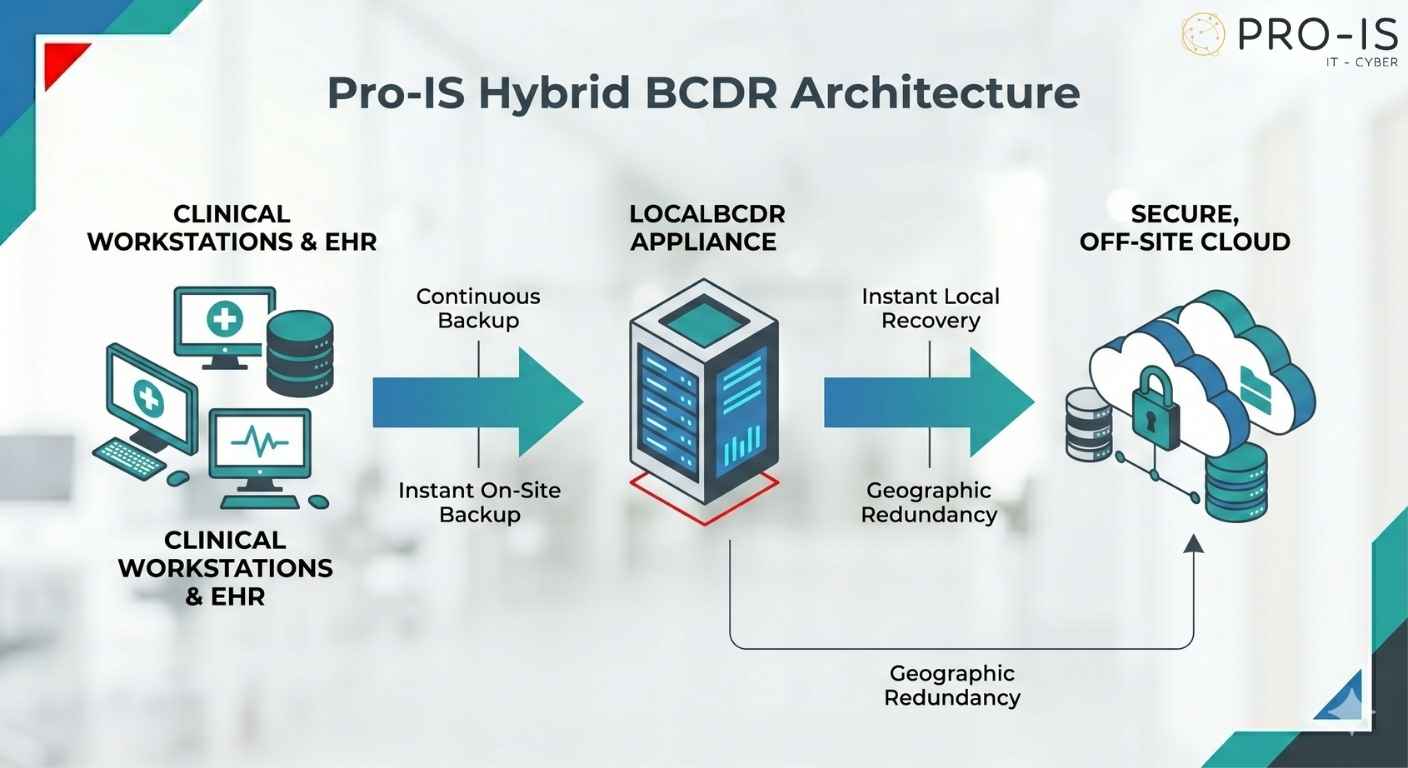
This dual-layer framework ensures optimal data protection and operational continuity:
- On-Site Resilience: If a primary server suffers a critical hardware failure mid-day, the local BCDR appliance instantly virtualizes the failed system. The clinic can resume operations within minutes, eliminating prolonged clinical downtime.
- Geographic Redundancy: Simultaneously, data is continuously mirrored to a secure cloud environment. In the event of a severe physical disaster—such as a facility fire or plumbing failure—the entire clinical network can be launched securely in the cloud, allowing staff to access vital systems from temporary locations.
Designing a Culture of Compliance: The Human Element
A technology stack is only as strong as the human beings operating it. Social engineering remains the most common method cybercriminals use to infiltrate secure medical networks. A distracted employee clicking a single malicious link in a fake “vendor invoice” or “password reset” email can bypass millions of dollars in defensive software.
The Imperative of Ongoing Security Awareness Training
Annual compliance training videos are no longer sufficient to counter modern digital threats. True human firewall protection requires continuous engagement:
- Simulated Phishing Environments: Managed IT partnerships should include regular, controlled phishing simulations that safely test staff members on real-world scenarios, identifying individuals who need additional coaching.
- Clear Protocols for Daily Operations: Staff must be continually trained on secure handling procedures, such as never sending unencrypted patient information via standard text message, utilizing secure email encryption tools for external referrals, and locking workstations whenever stepping away from patient areas.
Why Generic IT Support Fails Northern Colorado Healthcare Providers
Many independent practices contract their technology management to general computer repair shops or generic IT technicians. While these providers may be competent at replacing hardware or resolving basic network connectivity issues, they rarely understand the intricate operational realities and regulatory burdens unique to the healthcare vertical.
Choosing a generic IT vendor presents serious operational risks:
- The “Break-Fix” Trap: Traditional IT companies operate on a reactive model—they profit only when your systems break. For a healthcare practice, waiting for a system to fail before fixing it means accepting costly downtime, disrupted patient care, and potential data loss.
- The Business Associate Agreement (BAA) Gap: Under HIPAA regulations, any IT vendor accessing a network that contains patient data is legally defined as a Business Associate. Generic IT shops often refuse to sign a Business Associate Agreement (BAA), or they sign one without understanding that they assume direct legal liability for data security. Partnering with an IT provider that lacks a signed, comprehensive BAA places your entire practice in direct non-compliance.
Partnering for Peace of Mind with Pro-IS
True compliance and network security require a shift from reactive troubleshooting to proactive management. Pro-IS provides Northern Colorado’s business and healthcare community with a business-first approach to managed IT support, ensuring technology serves as a reliable asset rather than an operational bottleneck.
Our specialized, healthcare-focused IT management framework delivers comprehensive protection:
- 24/7/365 AI-Powered Monitoring: We look beyond traditional defensive tools by deploying continuous threat detection and remediation systems that identify and neutralize anomalous behavior before it disrupts clinical environments.
- Complete Compliance Mapping: We conduct rigorous, point-by-point security compliance audits to ensure your firewalls, access controls, email configurations, and backup systems align fully with current HIPAA security standards.
- Absolute Accountability: Pro-IS proudly stands alongside local practices as a trusted technology partner. We execute comprehensive Business Associate Agreements, confirming our shared commitment to safeguarding sensitive data.
Whether you operate an independent medical practice in Fort Collins, a specialized dental clinic in Greeley, or a veterinary hospital in Loveland or Boulder, your team deserves an IT infrastructure that works as hard as you do.
Protect your reputation, streamline your clinical operations, and secure your practice’s future by calling the local Pro-IS team today at (970) 613-0980 to schedule a no-obligation technology and compliance consultation.